IoT
Artificial Intelligence
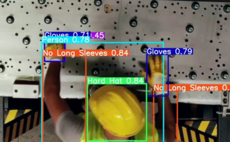
London-based startup Fogsphere uses standard 4K security cameras - the type that can be purchased for £70 - to monitor workplaces and create immediate alerts as soon as dangerous conditions are spotted.
Big Data and Analytics
'In two years it will be 45 million rows, easily'
Big Data and Analytics
Data analysis and a sprawling sensor network are saving money and boosting biodiversity
Chips and Components
And the person is 'recovering well'
Internet of Things
Haier claims the plugin is causing ‘significant economic harm’
Cloud and Infrastructure
The promise of the IoT is becoming a reality, finds Computing research
Networks
Economic incentives create dangerous levels of brittleness and a lack of adaptability in the face of rapid technological and market change
Threats and Risks
The flaw has also exposed the locations of a number of sensitive sites in the country.
Threats and Risks
EnemyBot is fast integrating exploits for recently announced vulnerabilities to improve its capabilities.

 23 July 2024
•
3 min read
23 July 2024
•
3 min read