“Business thinks IT has a crystal ball, but the truth is the CISO doesn’t always know what’s going on.”
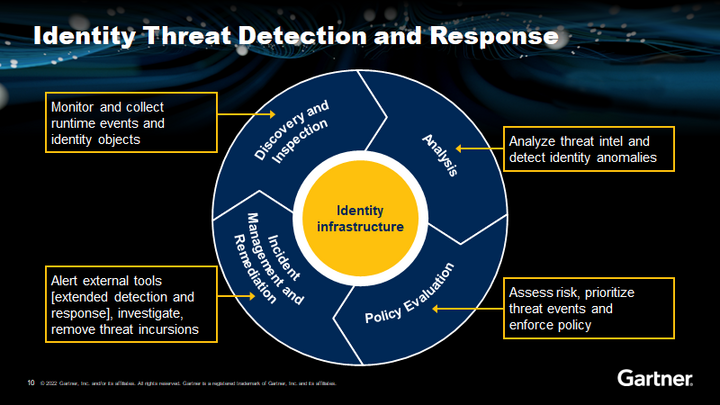
#2 Identity threat detection and response
"Identity is the new perimeter," said Furtado. "[It] is the crux of your network, the core of your network, and you need to have very strong identity discipline in your environments."
Weak identity discipline leads directly to things like credential compromise, which is still one of the main reasons companies are breached.
Action plan:
- Prioritise the security of identity infrastructure with tools to monitor, protect, detect and remediate.
- Use the MITRE ATT&CK framework (or similar) to correlate ITDR techniques with common attack scenarios.
- Invest in foundational IAM security best practices like least privilege.
- Modernise IAM infrastructure using current and emerging standards.
"We're seeing more and more organisations struggling simply from the fact that they don't do a good job with fundamentals. They don't do necessarily a good job of adapting their current models to be leveraged across their entire environment."