Samsung Galaxy S10 smartphone allows anyone to unlock devices when covered in third-party screen protectors
Natwest and Nationwide have withdrawn support for fingerprint authentication on the Samsung Galaxy S10 following reports that the sensor enables anyone to unlock a device.
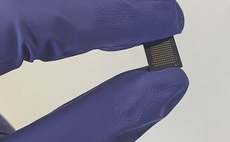
The under-display ultrasonic fingerprint reader glitch was uncovered last week. It enables anyone to unlock devices - not just the device's owner with their registered digit - if the display is covered with a third-party screen protector.
The glitch represents a particular vulnerability for users of Samsung Pay, the payment app that runs on the device and connects to people's regular bank accounts.
Natwest has already removed its banking apps from the Google Play Store for users of Galaxy S10 and S10+ devices, while Nationwide has disabled support for fingerprint authentication. Other banks, such as HSBC, have yet to follow suit.
"We've removed the app from the Play Store with customers with Samsung S10 devices," Natwest said in a message sent to affected users. "This is due to reports that there are security concerns regarding these devices. We hope to have our app available again once the issue has been resolved."
Those who already have the Natwest mobile banking app installed report that they're still able to login, but add that the fingerprint authentication option has been disabled - a measure also taken by Nationwide.
And users on Reddit claim that a number of financial services organisations across the world have also followed suit, with one person in Israel noting that their bank has disabled fingerprint login via their app, while another notes that their bank in the US blocked them from using Samsung Pay.
Samsung has acknowledged the issue and confirmed the fingerprint bypass vulnerability is affecting Galaxy Note 10, Note 10+, S10, S10+, and S10 5G models. The company has promised to release a software update to fix the glitch soon, after which users will need to rescan their fingerprints.
"Samsung Electronics is aware of the case of the S10's malfunctioning fingerprint recognition and will soon issue a software patch," the company said in a statement.